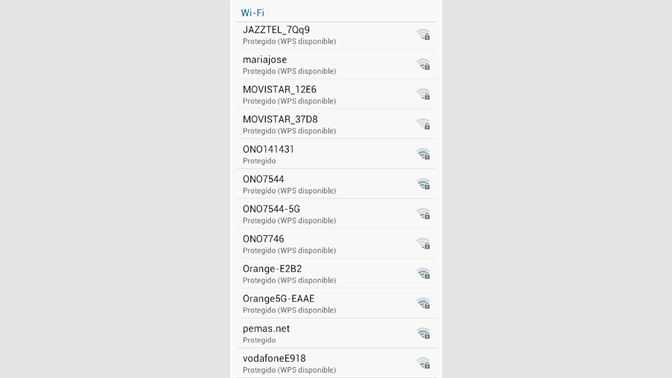
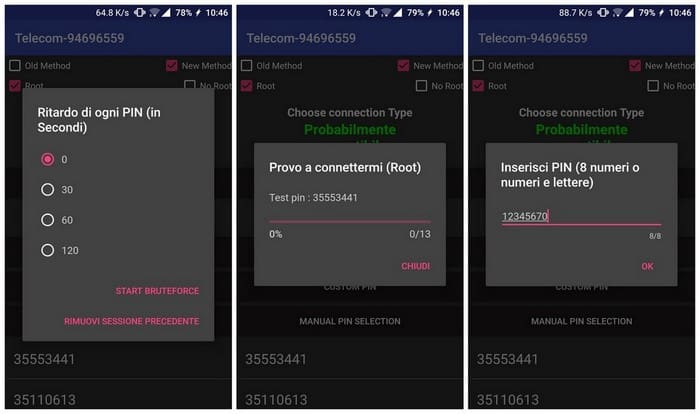
Here is a step by step guide how to hack to hack WiFi password using our tool. Step #1 - Download the app on your device and install it. Step #2 - Click the 'Scan for Available Networks' button and wait a moment until all SSID available networks are listed in a box below. Download cowpatty for free. CoWPAtty is designed to audit the security of pre-shared keys selected in WiFi Protected Access (WPA) networks.
- Wifi Hacking Tools For Windows 10 Free Download Utorrent
- Wifi Hacking Tools For Windows 10 Free Download Windows 7
- Best Hacking Tools Free Download
- Best Windows Hacking Tools
When I have started to learn
Today I can understand your condition if you are learning how to hack and still confused about hacking tools used by pro hacker and penetration tester then this post is relevant for you.
This is one of the most popular and famous programs out there to crack any wifi network. Once disconnected from the legitimate WiFi access point, the tool then force offline computers and devices to automatically reconnects to the evil twin, allowing the hacker to intercept all the traffic to that device. The technique is also known as AP Phishing, WiFi Phishing, Hots potter, or Honeypot AP.
Free Hacking tools for Information Gathering
#1 OSINT Framework
OSINT Framework This is not a tool but framework focused on gathering information using different tools available open source (over internet). The intention is to help people find free OSINT resources. Some of the sites included might require registration or offer more data for $$$, but you should be able to get at least a portion of the available information for no cost.
#2 SHODAN
SHODAN: Shodan also is not a tool, it is a search engine that lets the user find specific types of computers (webcams, routers, servers, etc.) connected to the internet using a variety of filters. Some have also described it as a search engine of service banners, which are metadata that the server sends back to the client.[1] This can be information about the server software, what options the service supports, a welcome message or anything else that the client can find out before interacting with the server.
#3 Check User Name
CheckUserName: It is an online service that helps hacker to check usernames more than over 170 social networks. This is especially useful if Hacker is looking for social media accounts with a specific username and helpful The penetration tester for running an investigation to determine the usage of the same username on different social networks.
#4 Google Dorks
GOOGLE DORKS: Hacker never forgets to gather useful information using the search engine Google. Google hacking is a technique to get information hidden in a deep search engine Database. Google Hacking Database is the collection of google dorks.
Google Dorks Tutorial Google Hacking | Open web information Gathering
Free Google Hacking Books: Google Hacking Filters Google Hacking for Penetration Tester
#5 Maltego
Maltego: Maltego is the passive information gathering tool condition if
Maltego Kali Linux Tutorial
#6 Recon-ng
Recon-ng: Recon-ng is another great tool pre-built in Kali Linux used to perform gathering information quickly. it is a full-featured Web Framework, it’s written in python. Complete with independent modules, database interaction, built-in convenience functions, interactive help, and command completion, Recon-ng provides a powerful environment in which open source web-based reconnaissance can be conducted quickly and thoroughly.
#7 Whois
A whois Kali Linux command is a utility as a part of the information gathering used in all of the Linux-based operating systems. this tool is part of information security assessment, and one of the information gathering techniques. there are a lot of information gathering strategies. It is used to identify domain information and more. Whois.com
#8 DIG (Domain Information Gropper)
Dig: The ‘dig command‘ is used in network administration that check and lookup domain name server (DNS) It is dnssec and the part of information gathering.
dnsenum
Find Information related Domain Name servers, mail servers, exchange server, file server etc.
#9 Theharvester
Theharvester: Grab email addresses by using it search engine database, it is mostly used to collect email details of particular domain. thehaverster in Kali Linux tutorial
#10 Creepy
Creepy: Creepy is a geolocation OSINT tool for penetration tester. Gathers geolocation related information from online sources by querying social networking platforms like Twitter, Flicker, and Facebook etc, and allows for presentation on map.
If anyone uploads images on social media with geolocation activated then you will see a full
It search filtering based on exact location and/or date, export in csv format or kml for further analysis in Google Maps.
Free Hacking tools for Network Scanning
#11 Nmap – A Network Scanner Free tool
Nmap is a free hacking tool and most used worldwide in terms of network scanning. It is used to detect live hosts in the network, open ports of devices, running service on the same port with version detail, also used for vulnerability scanning.
It is free tool and available for windows, Linux, Free BSD, OpenBSD, Solaris, IRIX, Mac OS X, HP-UX, NetBSD, Sun OS, Amiga, and more.
Nmap is a powerful tool, has been used to scan huge networks of literally hundreds of thousands of machines in the same network or the network
Some Important Tutorials Here
- Kali Linux Scan Network by
nmap pingsweep – [Full Guide]
#12 Angry IP Scanner
Angry IP Scanner is an open-source, simple and fast tool to use. It is a cross-platform network scanner.
It is widely used by network administrators, hackers, Penetration tester and just curious users around the world, including large and small enterprises, banks, and government agencies.
It is available for Linux, Windows, and Mac OS X, may be supporting other platforms as well.
It scans IP addresses and ports as well as has many other features as below:
- Scans local networks as well as Interne
- IP Range, Random or file in any format
- Exports results into many formats
- Extensible with many data fetchers
- Provides command-line interface
- Over 29 million downloads
- Free and open-source
- Works on Windows, Mac and Linux
- Installation not required
#13 Advanced IP Scanner
It provides remote control over computers using RDP and Radmin, and can even switch off computers.
It is available in a portable mode, you can have this tool in your pen drive.
#14 IP Scanner
It is
Features are:
- scan IP ranges automatically or on demand
- re-discover an entire subnet with just one click
- exclude devices from the results based on type or IP address
- import your entire network setup via a CSV file
- and do so much more!
#15 Hping3
It is available in Kali Linux by default it is one of DOS attack software, DDOS stand for distributed denial of service attack. you can launch and stop the DOS attack, whenever you want. In this illustration, hping3 will act as an ordinary ping utility, sending ICMP-reverberation und getting ICMP-reply
Tutorial Article: 10 hping3 examples for scanning network in Kali Linux
#16 NetDiscover
Netdiscover is an ultimate scanning tool used to get the internal IP address and MAC address of live hosts in the network. Netdiscover is a pre-installed tool in Kali Linux, if you are using Kali Linux then you don’t need to install
Must Read: 10 best open port checker Or Scanner
Vulnerability Assesment tools
#17 OpenVAS
OpenVAS does not default in Kali Linux if you want to use, you must install it first. It is available on the Kali Linux repository so you can install directly from the terminal using apt-get utility.
OpenVAS Documentation
The OpenVAS scanner is a comprehensive vulnerability assessment system that can detect security issues in all manner of servers and network devices.
Results will be delivered to your email address for analysis; allowing you to start re-mediating any risks your systems face from external threats.
Vulnerability scanning is a crucial phase of a penetration test and having an updated vulnerability scanner in your security toolkit can often make a real difference by helping you discover overlooked vulnerable items. For this reason, we’ve manually packaged the latest and newly released OpenVAS 8.0 tool and libraries for Kali Linux. Although nothing major has changed in this release in terms of running the vulnerability scanner, we wanted to give a quick overview on how to get it up and running.
#19 Nikto – Web Scanner
Nikto is
Nikto is an Open Source (GPL) web server scanner which performs comprehensive tests against web servers for multiple items, including over 6700 potentially dangerous files/programs, checks for outdated versions of over 1250 servers, and version specific problems on over 270 servers. It also checks for server configuration items such as the presence of multiple index files, HTTP server options, and will attempt to identify installed web servers and software. Scan items and plugins are frequently updated and can be automatically updated.
See All features of Nikto: https://cirt.net/Nikto2
Nikto Tutorial:
#20 Nexpose – Community Addition
Nexpose community vulnerability tool is developed by Rapid7 which is an open source tool. It is widely used for vulnerability scanning and a wide range of network intrusion checks. The following are the key features of Nexpose Community tool.
- The tool is quite detailed in its scanning where it takes into account the age of the vulnerability such as malware kit employed, the advantages taken by the kit, etc.
- The tool can be easily combined with a Metaspoilt framework.
- The tool is capable to scan the new devices in order to detect the vulnerabilities and evaluate the network.
- It can monitor the vulnerabilities exposures real time and can familiarize itself to the latest hazards very efficiently.
- The tool categorizes the risks post scanning for vulnerability into low, medium, or high scale.
Download Nexpose: Nexpose Comunity Adition
#21 Retina CS Community
Retina CS is an open source free vulnerability scanner tool. It is a web-based console. It is used
Features:
- The tool is good for network security administrators, help to saves both time and money required for network security management.
- It can perform automated vulnerability scans for workstations, web servers, web applications, and databases very swiftly.
- It can provide an assessment of cross-platform vulnerability.
- It has features to provide patching, configuration compliance, compliance reporting, etc.
- The tool supports virtual environments such as virtual app scanning, vCenter integration, etc.
Download: Retina CS Community Tool
Web Application Analyzing Tools
#22 WPscan
Wpscan a small tool written in ruby and preinstalled in Kali Linux, if you are using another Linux distribution, then install wpscan first.
Wpscan is used to scan the
WPscan Tutorial: WpScan
#23 HTTrack – Website Copier
HTTrack is a free (GPL, libre/free software) and easy-to-use offline browser utility.
It allows you to download a World Wide Web site from the Internet to a local directory, building recursively all directories, getting HTML, images, and other files from the server to your computer. HTTrack arranges the original site’s relative link-structure. Simply open a page of the “mirrored” website in your browser, and you can browse the site from link to link, as if you were viewing it online. HTTrack can also update an existing mirrored site, and resume interrupted downloads. HTTrack is fully configurable, and has an integrated help system.
WinHTTrack is the Windows (from Windows 2000 to Windows 10 and above) release of HTTrack, and WebHTTrack the Linux/Unix/BSD release.
See the download page. HTTrack Download
How to use
How to use
#24 Arachani Web Scanner
If you are Kali Linux user, then you shouldn’t worry about arachani web scanner is available for Kali Linux. Just run following command to install
#apt-get install arachni
The Arachni scanner is an escalated tool that runs from a web interface much likened to that of Tenable’s Nessus. Notwithstanding, dissimilar to Nessus, Arachni can just perform a scan against one host on one port at a time. On the off chance that there are different web services running on a host and not serviced from the port, then repeated scan will
Tutorial : How to use Arachni scanner for Web Application vulnerability in Kali Linux
#25 sqlmap – Database Enumerator
Sqlmap is default in Kali Linux, Use and enjoy to get important information from database server.
sqlmap is an open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over of database servers.
It comes with a powerful detection engine, many niche features for the ultimate penetration tester and a broad range of switches lasting from database fingerprinting, over data fetching from the database, to accessing the underlying file system and executing commands on the operating system via out-of-band connections.
Features :
- Supported databases are MySQL, Oracle, PostgreSQL, Microsoft SQL Server, Microsoft Access, IBM DB2, SQLite, Firebird, Sybase, SAP MaxDB, Informix, HSQLDB.
- Six sql injetion techniques support: boolean-based blind, time-based blind, error-based, UNION query-based, stacked queries and out-of-band.
- Direct connect to the database and enumerate data without DBMS credentials.
- It can dump databse tables.
- It support to download and upload any file from the database server underlying file system when the database software is MySQL, PostgreSQL or Microsoft SQL Server.
- the database server underlying file system when the database software is MySQL, PostgreSQL or Microsoft SQL Server.
Free Hacking tools for Password Cracking
#26 John The Ripper
John the Ripper is a fast password cracker, currently available for many flavors of Unix, Windows, DOS, and OpenVMS.
John, better known as John the Ripper, is a tool to find weak passwords of users in a server. John can map a dictionary or some search pattern as well as a password file to check for passwords. John supports different cracking modes and understands many ciphertext formats, like several DES variants, MD5 and blowfish. It can also be used to extract AFS and Windows NT passwords.
Documentation : https://www.openwall.com/john/doc/
#27 Hashcat
According to official website Hashcat is the world’s fastest CPU-based password recovery tool.
While it’s not as fast as its GPU counterpart oclHashcat, large lists can be easily split in half with a good dictionary and a bit of knowledge of the command switches.
Hashcat was written somewhere in the middle of 2009. Yes, there werealready close-to-perfect working tools supporting rule-based attackslike “PasswordsPro”, “John The Ripper”. However for some unknown reason,both of them did not support multi-threading. That was the only reasonto write Hashcat: To make use of the multiple cores of modern CPUs.
Granted, that was not 100% correct. John the Ripper already supported MPI using a patch, but at that time it worked only for
Must Read: Hashcat Tutorial – Bruteforce Mask Attack
#28 Cain and Abel
Cain & Abel is a password recovery tool for Microsoft Operating Systems. It allows easy recovery of various kind of passwords by sniffing the network, cracking encrypted passwords using Dictionary, Brute-Force and Cryptanalysis attacks, recording VoIP conversations, decoding scrambled passwords, recovering wireless network keys, revealing password boxes, uncovering cached passwords and analyzing routing protocols.
Cain and Able Tutorial:
#29 Hydra-THC
According to official website of thc-hydra, One of the biggest security holes are passwords, as every password security study shows. This tool is a proof of concept code, to give researchers and security consultants the possibility to show how easy it would be to gain unauthorized access from remote to a system and different online services
There are already several login hacking tools available, however the online services Either support more than one protocol to attack or support panellized Connects.
THC-Hydra Tutorial: Dictionary attack tool thc-hydra tutorial for beginner
#30 FcrackZip
fcrackzip searches each zipfile given for encrypted files and tries to guess the password. All files must be encrypted with the same password, the more files you provide, the better.
Have you ever mis-typed a password for unzip? Unzip reacted pretty fast with ´incorrect password´, without decrypting the whole file. While the encryption algorithm used by zip is relatively secure, PK made cracking easy by providing hooks for very fast password-checking, directly in the zip file. Understanding these is crucial to zip password cracking.
Tutorial: Fcrackzip Windows to crack zip password [Tutorial]
Must Read: Top 10 Password cracker software for Windows 10
Free hacking tools for Wi-Fi
#31 Aircrack-ng
Aircrack-ng is not a tool, but it is a complete set of tools including used to audit wireless network security.
It focuses on different areas of WiFi security:
- Monitoring: Packet capture and export of data to text files for further processing by third party tools
- Attacking: Replay attacks, deauthentication, fake access points and others via packet injection
- Testing: Checking WiFi cards and driver capabilities (capture and injection)
- Cracking: WEP and WPA PSK (WPA 1 and 2)
All tools are command line which allows for heavy scripting. A lot of GUIs have taken advantage of this feature. It works primarily Linux but also Windows, OS X, FreeBSD, OpenBSD, NetBSD, as well as Solaris and even eComStation 2
Aircrack-ng Documentation: https://www.aircrack-ng.org/doku.php#documentation
#32 Fern Wifi Cracker
Fern Wifi Cracker is GUI (Graphical User Interface) based tool. It is easy to use. If you are not command lover person then this is a best tool for you to crack wifi including WEP/WPA/WPA2.
Fern Wifi Cracker is a Wireless security auditing and attack software program written using the Python Programming Language and the Python Qt GUI library, the program is able to crack and recover WEP/WPA/WPS keys and also run other
Features:
- WEP Cracking with Fragmentation,Chop-Chop, Caffe-Latte, Hirte, ARP Request Replay or WPS attack
- WPA/WPA2 Cracking with Dictionary or WPS based attacks
- Automatic saving of key in database on successful crack
- Automatic Access Point Attack System
- Session Hijacking (Passive and Ethernet Modes)
- Access Point MAC Address Geo Location Tracking
- Internal MITM Engine
- Bruteforce Attacks (HTTP,HTTPS,TELNET,FTP)
- Update Support
Best Tutorial : Fern WiFi Password Auditing Tool
#33 Fluxion
Fluxion is a wifi Security analysis tool security study
Complete Tutorial: Fluxion – WPA WPA2 hacking in minutes [2019]
#34 Metasploit Framework
If you are planning to learn hacking, you must learn how to use metasploit framework.
Metasploit is as important as milk for body.
It is the collection of small tool or scripts used for scanning, enumeration, vulnerability scanning, exploitation, password cracking, maintaining access and more.
You can say one framework collection of tool
Metasploit framework Version v5.0.2-dev has
- 1852 exploits
- 1046 auxiliary
- 325 post
- 541 payloads
- 44 encoders
- 10 nops
- 2 evasion
Metasploit is easy to learn and use for Hacking or penetration testing. Command line interface makes it more strong and powerful.
You can write your own exploits and use inside metasploit. It is absolutely Free.
Metasploit Tutorial Links:
Metasploit Unleashed by Offensive Security
Metasploit Minute by Hak5 Team
Free Metasploit Course by Cybrary
#35 Armitage
Do Easy and fast hacking with Armitage It is graphical interface of Metasploit framework. It has user friendly interface. Everything in one click.
One click for scanning network.
One Click for run vulnerability scanning, possibilities of exploitation those weakness.
One Click for creating backdoor and more.
Really it is very awesome exploitation framework you must try and use it.
Armitage Tutorial: Manual Page
#36 BeEF – Exploit Browser
BeEF is short for The Browser Exploitation Framework. It is a penetration testing tool that focuses on the web browser.
Amid growing concerns about web-borne attacks against clients, including mobile clients, BeEF allows the professional penetration tester to assess the actual security posture of a target environment by using client-side attack vectors. Unlike other security frameworks, BeEF looks past the hardened network perimeter and client system, and examines exploitability within the context of the one open door: the web browser.
BeEF will hook one or more web browsers and use them as beachheads for launching directed command modules and further attacks against the system from within the browser context.

Beef Youtube Channel: https://www.youtube.com/user/TheBeefproject
Blog : https://blog.beefproject.com/
#37 SET – Social Engineering Toolkit
It is time to exploit human, Yes human can be exploited through the computer. Just send a link to him/her, He/she will give you personal information (some time username and password) try it now.
This is menu based exploitation framework, It means choose the option from given menu, choose again and again. Hurrrr you launched attack.
It is very usefull for hacking social media accounts like Facebook, twitter, LinkedIn etc.
Do you want hack Gmail account use it.
Hacker can hack facebook account in 1 MinuteSubscribe Youtube channel:https://www.youtube.com/channel/UC7nTdoS8d0bmiVUrQTjpuzwPlease share someone Who has requirements for this training. Hacking Group: https://www.facebook.com/groups/cyberpratibhaRegards!Vijay Kumar
Posted by Cyrage on Thursday, 19 April 2018#38 Macchanger
macchanger is a GNU/Linux utility for viewing/manipulating the MAC address for network interfaces.
MAC address is a physical address of NIC (Network Interface Card).
Every device in the network has two type of address, One is IP address another MAC address. IP address can be changed easily, but MAC address can’t.
Macchanger is used to change the MAC Address of devices. It is available only for Linux.
It comes in Kali Linux by default.
More: Learn about macchanger or MAC spoofing in Windows 10 & Linux
#39 ArpSpoof
arpspoof redirects packets from a target host (or all hosts) on the LAN intended for another host on the LAN by forging ARP replies. This is an extremely effective way of sniffing traffic on a switch
Kernel IP forwarding (or a userland program which accomplishes the same, e.g. fragrouter(8)) must be turned on ahead of time
#40 Ettercap – MITM AttacK
Man In The Middle attack is very famous attack performed by hacker. In this attack hacker sit between you and server, and monitor all the network traffic between you and servers on the internet.
Hacker can see what are you browsing, what text you are filling on which website. If you are entering username and password, it can be seen. So be careful about this attack.
Ettercap is a comprehensive suite for man in the middle attacks. It features sniffing of live connections, content filtering on the fly and many other interesting tricks. It supports active and passive dissection of many protocols and includes many features for network and host analysis
#41 Wireshark
Wireshark is a shark of network monitoring / capturing each every packet traveling over wire or wireless medium.
Using wireshark is enough for a network administrator / Network security researcher to monitor network activity.
Wireshark is the world’s foremost and widely-used network protocol analyzer. It lets you see what’s happening on your network at a microscopic level and is the de facto (and often de jure) standard across many commercial and non-profit enterprises, government agencies, and educational institutions. Wireshark development thrives thanks to the volunteer contributions of networking experts around the globe and is the continuation of a project started by Gerald Combs in 1998
Features:
- Deep inspection of hundreds of protocols, with more being added all the time
- Live capture and offline analysis
- Standard three-pane packet browser
- Multi-platform: Runs on Windows, Linux, macOS, Solaris, FreeBSD, NetBSD, and many others
- Captured network data can be browsed via a GUI, or via the TTY-mode TShark utility
- The most powerful display filters in the industry
- Rich VoIP analysis
- Read/write many different capture file formats: tcpdump (libpcap), Pcap NG, Catapult DCT2000, Cisco Secure IDS iplog, Microsoft Network Monitor, Network General Sniffer® (compressed and uncompressed), Sniffer® Pro, and NetXray®, Network Instruments Observer, NetScreen snoop, Novell LANalyzer, RADCOM WAN/LAN Analyzer, Shomiti/Finisar Surveyor, Tektronix K12xx, Visual Networks Visual UpTime, WildPackets EtherPeek/TokenPeek/AiroPeek, and many others
- Capture files compressed with gzip can be decompressed on the fly
- Live data can be read from Ethernet, IEEE 802.11, PPP/HDLC, ATM, Bluetooth, USB, Token Ring, Frame Relay, FDDI, and others (depending on your platform)
- Decryption support for many protocols, including IPsec, ISAKMP, Kerberos, SNMPv3, SSL/TLS, WEP, and WPA/WPA2
- Coloring rules can be applied to the packet list for quick, intuitive analysis
- Output can be exported to XML, PostScript®, CSV, or plain text

Tutorial for Beginners: Using Wireshark
Download Wireshark: https://www.wireshark.org/#download
Wireshark Tutorial: Wiki
Wifi Hacking Tools For Windows 10 Free Download Utorrent
#42 Burp Suite Community
Burp Suite is the leading software for web security testing…
Thousands of organizations use Burp Suite to find security exposures before it’s too late. By using cutting-edge scanning technology, you can identify the very latest vulnerabilities. Our researchers frequently uncover brand new vulnerability classes that Burp is the first to report
Burp Suite constantly raises the bar of what security testing is able to achieve.
Download Burpsuite Community edition : Download Here
Tutorial of Burp Suite: Web Security
#43 Owasp ZAP Prox
The OWASP Zed Attack Proxy (ZAP) is one of the world’s most popular free security tools and is actively maintained by hundreds of international volunteers*. It can help you automatically find security vulnerabilities in your web applications while you are developing and testing your applications. Its also a great tool for experienced pentesters to use for manual security testing.
Official Website Owasp ZAP
#44 Dardis – Report Writing
When you are working as a Penetration tester/ Ethical hacker / Security Researcher then You must submit report to the organization about issues or vulnerabilities.
So you must know to to write report and send to organization.
It comes with kali linux by default if you are not user of Kali Linux then you can download from Here
If Appreciate My Work, You should consider:
- Join Group for Discussion Facebook Group
- Get your own self-hosted blog with a Free Domain at ($2.96/month)
- Buy a Coffee to Us! Make Small Contribution by Paypal
- Support us by taking our :Online Courses
- Contact me :[email protected]
Are you looking for a Windows Application that will let you hack Wi-Fi using your Laptop, whether you are at home or you are traveling, are you tired of those free Wi-Fi hacking and password revealer software that claim they can hack any Wi-Fi password only to find out they are dummy only after downloading them?
Related:
Then this post we are beneficial to you, this is because we have reviewed some of the best Wi-Fi password hacking software that is compatible with your Windows XP/Vista/7/8/8.1 and Windows10 PC.
WiHack
It’s one of the frontrunners of Wi-Fi hacking software scene & was originally developed as some special project that would work with locked wireless networks. It can help you with a number of functions like getting users list, cracking the Wi-Fi password, see each user’s movement as well as block off the unwanted users from Wi-Fi network.
Aircrack-ng
It deals with various aspects concerning Wi-Fi security. It can monitor data export to the text files, replay attacks, deals with deauthentication through packet injections etc. then, it will check the Wi-Fi cards & driver capabilities as well as crack the WEP & WPA PSK.
Kismet Wireless
Kismet Wireless is a popular wirefree network detector, intrusion detection & sniffer system. It mostly deals with IEEE 802.11 Wi-Fi networks yet can also tackle other networks. Its great range of features include server/client modular architecture, PCAP logging, multi capture-source support, remote sniffing as well as XML output that will help easy integration with the other tools.
inSSIDer
inSSIDer is your ally when it comes to troubleshooting Wi-Fi issues. This Wi-Fi optimization & troubleshooting program will help you with a number of things- weak channel placement, poor signal strength, RF interference problems in 2.4 & 5 Giga Hertz bands. It comes in 2 versions- inSSIDer 4 & inSSIDer Office.
AirSnort
This is another major wi fi hacker software program that has been highly rated by the users. This wireless LAN program can crack the encryption keys efficiently on the 802.11b WEP Wi-Fi networks. The software operates through passive monitoring of the transmissions, computing encryption key while adequate packets are gathered.
Wifi Hacking Tools For Windows 10 Free Download Windows 7
Wireshark
Wireshark is quite a big name here and comes with multiple amazing features. These include deep inspection on numerous protocols, handy 3-pane packet browser, live capture & offline analysis, multi platform running capacity, enriched VoIP analysis, reading/writing of various capture file versions etc. In other words it offers you a deep insight on the network.
WepAttack
This list would be incomplete without the mention of WepAttack. Just as the name suggests, it’s a powerful tool that will help you to launch a sizeable attack on the WEP keys of the WLAN networks. The users are really happy with the software and many of them have tagged it as one of the best for cracking passwords.
Wi-Fi Hacking Software for Various Platforms
You should know here that there are different email address management software applications for various platforms. The one you would be going for must complement your system’s specific OS. Not all such software applications would work for all operating systems and you have some software programs that specifically work for Windows or Android or Mac.
Free Windows Wifi Hacking Software – OmniPeek
If you are looking for a good free Windows Wifi hacking software, OmniPeek is a great choice. It’s an award winning network analyzer & packet sniffer application that captures & analyzes the wireless traffic. The tool is equipped to work with several networking interface cards. You will also get help on network troubleshooting.
Free Android Wifi Hacking Software – Black Wi-Fi Hacker
When it comes to reliable Free Android wifi hacking software, Black Wi-Fi Hacker Plus is a good option no doubt. The software is designed to crack Wi-Fi networks locally, assuring a seamless access for you to the network. The program supports multi encryption types such as WPA, WPA2, WEP or CCMP/AES encryption.
Free Mac Wifi Hacking Software – KisMAC
Those in search of free Mac Wifi hacking software, KisMAC would be a nice choice. It’s an open-source Wi-Fi scanner/stumbler application, which, unlike other regular Wi-Fi hacker software applications, uses passive scanning & monitor mode. The program reveals closed or cloaked or hidden SSIDs, shows the logged in users, helps with PCAP import & export etc.
Most Popular Wifi Hacking Software for 2016 – Wi-Fi Hacker
Best Hacking Tools Free Download
You are getting a very simple, user-friendly yet powerful Wi-Fi hacking software here. It would quickly search out the local available Wi-Fi network & connect you to it so that you can bypass the locked Wi-Fi route in moments. It is virus free & gets updated just automatically, making things simpler for you.
When it comes to most popular Wifi hacking software for 2016, you can opt for Wi-Fi Hacker .The user-friendly software program is well equipped to hack both WPA & WPA2 as well as WEP and promises you good support against the WPS attack. Its virus-free nature is one of the main reasons for its popularity today.
What is Wi-Fi Hacking Software?
A Wi-Fi hacking software is a software program that will primarily enable you to crack Wi-Fi password of a nearby network. These software programs are designed to work for WPA, WPA2 and WEP. Some of them are open-source applications and work as good network analyzer as well as packet sniffer.
The best ones are guarded against the WPS attack. A good lot of Wi-Fi hacker software applications are meant to help with Wi-Fi troubleshooting issues. In simple words, these software programs are your key to Wi-Fi internet freedom where you won’t need to ask for the permission of the network administrator to access the desired router.
How to Install Wi-Fi Hacking Software?
To install Wi-Fi hacking software, you have to go to the chosen software’s link to download it. However, before you download, just make sure that the software program actually complements your specific operating system. When you download it, you will get the installation link that will come up with a complete guide on installing the application.
Best Windows Hacking Tools
Benefits of Wi-Fi Hacking Software
Many a times, we find ourselves in places where we desperately need the Wi-Fi for an urgent communication or quick internet search but we cannot access the local router given no knowledge of the password. In such situations, the Wi-Fi hacking software is just a bliss.
Such software applications would immediately crack the Wi-Fi password for you, in most of the cases of any strength, so that you can freely access the internet. The software program would also be helpful for network auditors and penetration testers who have to verify security of the WPA guarded wireless networks, break document encryption and crack the password hashes.
The Wi-Fi hacker software applications would be helpful when you are looking to check what’s going on with the Wi-Fi network of your organization and what the users are doing with the network. All such software applications are really easy to operate and your primary computing skills would be enough here.